Protecting FileMaker Platform Business Solutions
Protecting FileMaker Platform Business Solutions
FileMaker Platform developers and FileMaker Server Administrators, as well as business data owners, need to take a variety of steps to protect the Confidentiality, Integrity, Availability, and Resilience (CIAR) of their FileMaker Platform Business Solutions. Threat Agents of many varieties seek to exploit vulnerabilities that might exist in those solutions to compromise them, to steal data, to alter data, or to destroy data.
This FileMaker Security BLOG article will describe four key steps that developers and administrators can take to protect their files. Before listing those however, I want to describe an important caveat about such an approach to FileMaker platform security.
Security is never a case of “One and Done.” It is not a check list of things to do to files, and then they are and will remain secure. Business circumstances change. We discover new vulnerabilities. Threat Agents perfect new attacks, some possibly exploiting so-called Zero Day vulnerabilities. Security is an on-going process in a constant state of flux. Maintaining security for business solutions requires constant monitoring and evaluation. All that said, however, here are four important considerations. All employ tools that the FileMaker platform already gives us to help protect our files.
First. Use Granular Access Privileges. The FileMaker security schema allows for very specific privileges as well as for very broad ones. For best protection and control, set the privileges and permissions for each Privilege Set very carefully. For each business role, give the users in that role all the privileges they need for them to accomplish their business requirements. But do not give them any added privileges. This is called the Rule of Least Privileges, and it is fundamental to having correct security for your files.
This process may take a bit of work, and it requires you to know and to understand what users are supposed to be doing—and not doing—in the file. To do this you also need to know what permissions are on and which are off by default in each Privilege Set. When a developer creates a new Privilege Set in a file, most privileges bits are off or at their most restrictive settings by default. This is a correct and is a consistent behavior with the Rule of Lest privileges. One of the things a developer wants to achieve in working with the security schema is to prevent an otherwise authorized user from escalating his or her privileges and gaining a level of access above the prescribed one.
To that end, developers should most likely avoid in almost all situations the use of the two default subordinate level Privilege Sets: [Data Entry Only] and [Read-Only Access]. Both these contain privileges in excess of what their names suggest. If you plan to use them, carefully review the actual privileges they grant to see if those are consistent with your security model.
Second. Invoke Encryption at Rest (EAR) on your files. This is a particularly important step; likewise, EAR offers particularly good protection, provided you use a strong encryption password. FileMaker Pro will tell you the strength of the password: Weak, Moderate, or Strong. If someone gains access to a copy of your files by any of several attack vectors, EAR prevents their forcing the file open or employing any of the so-called “password crackers” on them. Unauthorized possession of copies of files, including backup copies, is a particularly strong attack vector. It is also an attack vector that Threat Agents frequently employ.
Third. Use File Access Protection to block manipulation of your files by other FileMaker Pro files you do not control. File Access Protection prevents unauthorized persons from pointing their files at yours and extracting, viewing, or manipulating information.
An important part of effective file protection is understanding how external Application Program Interfaces (API’s) can access your FileMaker Pro business solutions and then how to control that access. This includes layout access, file metadata, and the business logic found in scripts. [You can read more about this topic here: http://fmforums.com/blogs/entry/1535-the-filemaker-platform-api’s-are-your-friends-right/]
Some of these elements respond to fine-grain permission controls in the Privilege Set. Others do not; hence, developers should utilize File Access Protection. Additionally it can assist in preventing users who are otherwise authorized a particular level of permissions from escalating those permissions and privileges in the file. Escalation of privileges is a key vulnerability we must try to prevent in all instances.
Fourth. Utilize Encryption in Transit to protect you data while they are in motion between FileMaker Server and a variety of FileMaker Platform clients such as WebDirect™, FileMaker GO, and FileMaker Pro. This is particularly important when users are accessing FileMaker Platform Business Solutions by public Wi-Fi networks such as those found in coffee shops, hotels, conference centers, malls, airports, and similar venues. For that matter it is also important when the only access is across a Local Area Network (LAN) behind a closed firewall. Just one single rogue wireless access point on that LAN can compromise it. Additionally anyone with access to the LAN could also intercept data in transit. Encryption in Transit also helps verify the identity of the FileMaker Server and helps prevent man-in-the-middle attacks where a Threat Agent could impersonate your FileMaker Server.
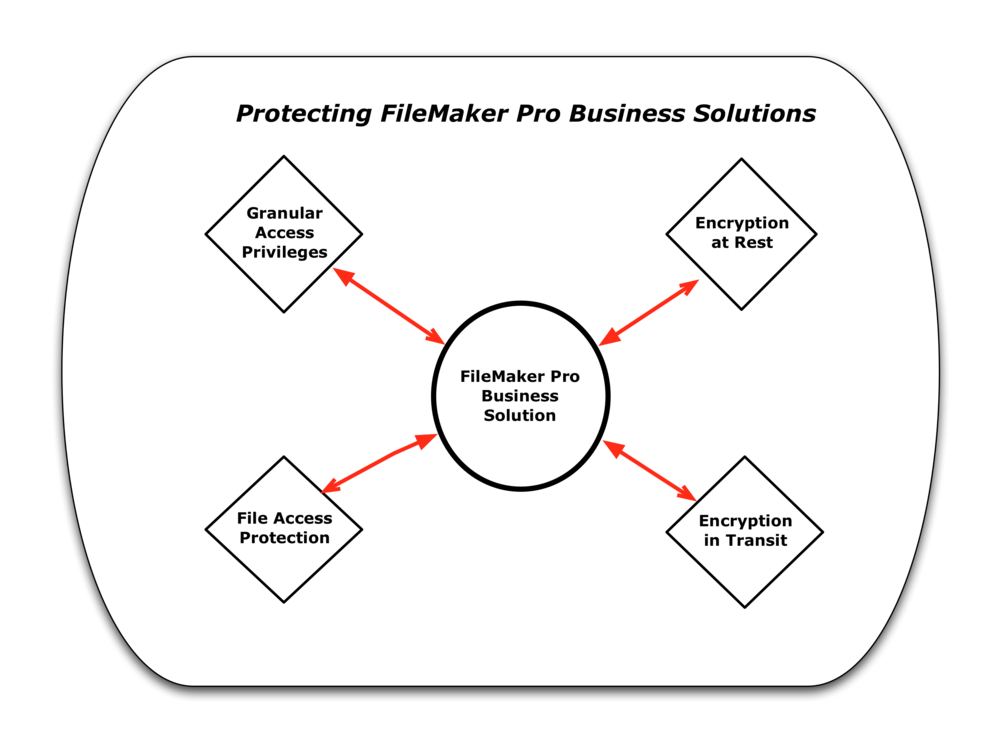
I have described four FileMaker Platform security tools that developers and administrators can use to protect FileMaker Platform business solutions:
Granular Access Privileges
Encryption at Rest
File Access Protection
Encryption in Transit
I have attached a schematic that can serve as a reminder about these features. Remember when using these, that security is dynamic and on-going. It is never a “One and Done” scenario. The FileMaker Platform provides these tools. A number of people have done a very considerable amount of work over the years to add these to the FileMaker Platform. I strongly recommend their use.






Recommended Comments