Stop Adapting. Start Building. FileMaker Pro.

What Is FileMaker Pro?
by Kurt Knippel,
Project Manager / VP of Production
In a world crowded with business apps, few platforms have achieved the longevity, adaptability and loyal following of Claris FileMaker Pro, which has been solving real business problems for more than 40 years.
Developed and maintained by Claris International, an Apple subsidiary, FileMaker Pro is a low-code, custom application development platform. Yes, it’s a powerful relational database system — but calling it a database tool is like calling a heavy-duty fleet vehicle a cup holder on wheels.
Claris FileMaker Pro lets you build custom, professional-grade software solutions tailored to your unique workflows, making it the perfect platform for custom solution development for small and medium-sized businesses, or SMBs. Did we mention it’s user-friendly so you don’t need a traditional programming team to code it?

Filemaker’s easy-build formula includes:
- An intuitive drag-and-drop interface made for business owners and everyday users
- Built-in scripting
- Visual design tools
Need a system for:
- Contacts and customers
- Inventory tracking
- Quoting and invoicing
- Scheduling or event registration
- Project management
- Or a full operations hub tying everything together
Filemaker can power it!
A Platform That Works Everywhere You Do
Filemaker has true cross-platform compatibility, running natively on:
It’s also accessible through any web browser via WebDirect – no additional web programming required, or utilize Custom Web Publishing. Whether your team member is on an office desktop, in the field on an iPhone, or working remotely from a laptop, they can connect to the same live data in real time.
The ecosystem includes:
- FileMaker Pro — The main software on your Mac or PC where your custom business app is built and used
- Claris Go — For mobile access on iPhone or iPad (think remote workers)
- FileMaker WebDirect — Runs your custom app in a web browser
- FileMaker Server — Host internally
- FileMaker Cloud — A cloud-hosted option
- Claris Studio — A newer addition to the platform enabling web-based forms, dashboards, kanban boards, and data views that integrate directly with FileMaker
- Claris Connect — For workflow automation with third-party tools (i.e., Slack, MailChimp, Box, and more)
Since the 2025 release, all capabilities come bundled into one unified platform license, making custom solution development more accessible for SMBs than ever before.
Built for SMB Flexibility, Security and Growth
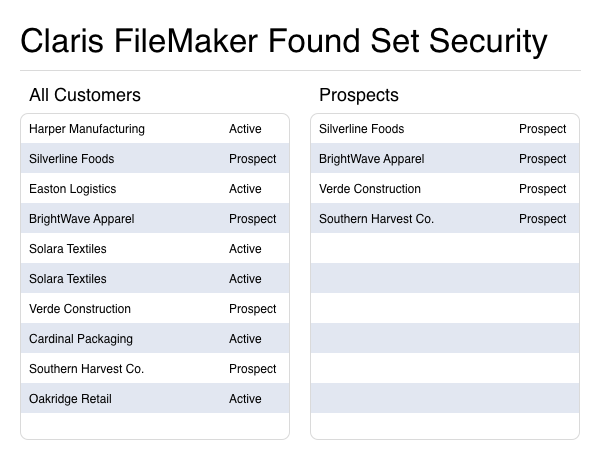
FileMaker Pro is designed with clean, efficient code built to handle record locking, lightning-fast searches over large data sets, and robust multi-user environments. It offers enterprise-grade security with 256-bit encryption, granular user access controls, and strong authentication options.
As your business grows, your FileMaker solution grows with it. New fields, tables, layouts, scripts and integrations can be added incrementally without rebuilding from scratch. This scalability makes FileMaker equally viable for a five-person team and a multi-location organization with hundreds of users.
Why Businesses Like It
Filemaker lives in the sweet spot between the two software eXtremes – SaaS and custom builds. Off-the-shelf SaaS solutions offer convenience but impose limitations, often forcing you to work within someone else’s feature set, pay for capabilities you may not need, and abandon workflows that have made your business successful. Custom enterprise software, on the other hand, is eXpensive and requires long development timelines and dedicated IT teams.
FileMaker Pro occupies a uniquely powerful middle ground.
Your Business, Your Rules
With Filemaker, you can build custom software tailored to your business needs.
Your workflow.
Your processes.
Your terminology.
Your reporting needs.
Your approval chains.
Your rules!
AI Is Now Built In
FileMaker’s latest release includes native AI capabilities such as deep integration with Large Language Models, including support for OpenAI, Anthropic and open-source models that can run locally on your own hardware, keeping sensitive business data private.
What this means for small businesses:
- Natural language search — Ask your database questions in plain English without needing to know how to write searches or SQL
- Sentiment analysis — Let AI automatically analyze customer feedback, support tickets or survey responses flowing through Claris Studio web forms
- Intelligent automation — Pre-written AI-generated responses, summaries and recommendations can be triggered automatically within your workflows
- Semantic search — Find records based on meaning and context, not just eXact keyword matches
- PDF text eXtraction — Pull data/content from PDFs stored in your database
These capabilities, once reserved for companies with dedicated engineering resources, are now accessible to anyone running FileMaker – including YOU!
Rapid Development Means Faster ROI
Speed matters to SMBs. With Filemaker Pro’s low-code approach, you can go from idea to working solution in days or weeks – not months.
That means you can adapt quickly to new demands, fix bottlenecks and capitalize on opportunities without waiting on a long development cycle.
For businesses that run lean, Filemaker’s rapid development cadence is a strategic necessity. Every eXtra week you run a manual process it costs you money in labor and missed opportunities, not to mention the errors that may be introduced without automation.
FileMaker helps you close that gap – FAST!
Check out some of our client success stories.
Filemaker Plays Nicely With Others
A key part of custom solution development for SMBs is connecting systems — not replacing everything.
FileMaker connects with the tools businesses already use:
- QuickBooks (and other accounting platforms for financial data synchronization)
- E-commerce systems (WooCommerce, Magento, Shopify)
- Shipping APIs (FedEx, UPS, USPS)
- Payment processors (PayPal, Stripe)
- Google services (Maps, Calendar, Workspace)
- Email platforms and phone systems
- Amazon, eBay and other marketplace integrations
- Microsoft SQL Server, Oracle, MySQL, PostgreSQL (for enterprise data connections)
- Cloud services (Slack, MailChimp, Box; no custom integration code needed)
Deployment That Fits Your Infrastructure
FileMaker meets you where you are. Deploy on-premise with FileMaker Server for maximum control, move to the cloud with FileMaker Cloud for flexibility and reduced IT overhead, or choose a hybrid approach. The platform supports Ubuntu 24 server environments and integrates with AWS, adding more options for businesses with eXisting cloud infrastructure. SSL certificate management has also been dramatically simplified in the latest release, reducing the burden on non-technical administrators.